Apparently I never posted about the latest changes. Most of this was back in September before fall TV started up…
My “Knoppmyth”:http://mysettopbox.tv/knoppmyth.html installation was getting a little old and decrepit, even after the update for Schedules Direct. These days I use “Ubuntu”:http://ubuntu.com/ on all of the servers, so with the second release of “Mythbuntu”:http://www.mythbuntu.org/ available I decided it was time to switch the PVR.
The first upgrade was relatively painless. I started with Mythbuntu 7.10, because it used the same “MythTV”:http://www.mythtv.org/ version as my Knoppmyth install. First I installed onto my spare 160Gb drive; I have two, because I was originally planning to use RAID-1 on the PVR. Alas, the extra CPU and I/O required was too much for my wimpy PIII-933, so now I have a spare.
I was able to copy and/or merge most configuration files from the old setup to the new, since they were based on similar Debian releases. There were a couple of problems with TV-out on my ancient Matrox G400 card; once again vesafb was loading and blocking the Matrox drivers. At least this time they were both already modules, so I did not have to recompile the whole kernel! Then I restored the MySQL databases from backup and copied the video files over (that took a few hours). I tested the machine for about a week, and it was working fine.
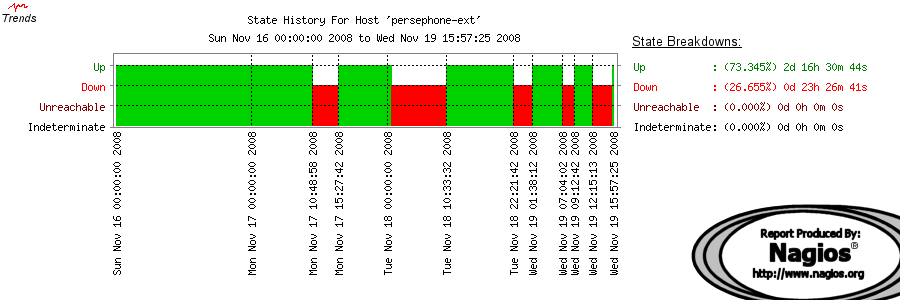
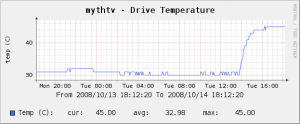
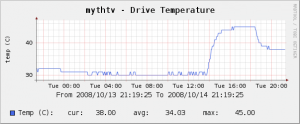
Unfortunately, the upgrade to Mythbuntu 8.04 did not go as well. For some reason, the latest kernels would not boot on my old Compaq Deskpro! I never did figure out why. Since the cooling fans in that machine were dying anyway, I decided to swap in the old Baltimore Dell workstation that Andrzej gave me last year. I happened to have a spare CPU in the parts box, so I now have a PVR with two PIII-933 CPUs, making the box a little snappier when watching TV while recording.
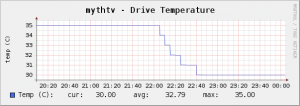
Of course, about a week later, the Dell fan started chirping (as I posted about previously). Then my cheapo UPS died, and the Dell kept shutting itself down until I plugged it directly into the wall. Now everything is stable (and cool) again, and I’m quite happy to be running the same linux version on all six servers! (I don’t have _that_ many computers at home; four of those “servers” are virtual machines, two of them at hosting facilities in Atlanta GA…).
So, that’s it until next spring, after May sweeps, by which time Mythbuntu 9.04 will be out :-).
*Update 2009/05/28:* 1) the upgrade to 9.04 was uneventful. 2) My old server died, so I had to buy a new (old) computer. In the process of swapping hardware around, I had the “would not boot” problem again. I eventually discovered that my earlier problems with kernels not booting was not caused by the motherboard, but by the particular Matrox G400 that was in the old Compaq Deskpro. That was a day wasted, trying to get the right combination of hardware into one machine :-).
Arrington is such a whiner. The things he complains about are kinda obvious aren’t they? And some seem to be just his problem – eg not being able to scroll down without looking down at the kbd/mousepad. And I can’t believe 80% of a regular-sized keyboard isn’t easier to use than a blackberry-sized one for reasonable values of finger-size. As for speed you’re clever enough to install and use a version of Linux that would be sufficiently stripped down to be useable, no? Then again I seem to remember you’re not a big desktop linux fan…
I’m a fairly heavy desktop user, and so my dislike of desktop Linux reflects that. Audio doesn’t work properly, the UI is inconsistent (at best, and unusable at worst :), and so on as reflected in many rants on the ‘net. It’s been getting better and better, but usability has always been open-source’s Achilles Heel.
A netbook is a different beast, though; for me, it’s really a portable browser, with some local storage for simple documents and things like photo backup. And a Linux-based OS (especially something like Splashtop) is perfect for this environment, where Windows would be over-kill (and too bloated to run on a small device).
I was already aware of the limitations of the screen and keyboard; I’m just not yet convinced that I would be able to put up with them. And for casual use, I don’t really want to spend $400CDN :)